The EU General Data Protection Regulation (GDPR) is among the world’s toughest data protection laws. Under the GDPR, the EU’s data protection authorities can impose fines of up to up to €20 million (roughly $20,372,000), or 4% of worldwide turnover for the preceding financial year – whichever is higher.
Since the GDPR took effect in May 2018, we’ve seen over 900 fines issued across the European Economic Area (EEA) and the U.K. GDPR fines have ramped up significantly.
Let’s take a look at the biggest GDPR fines, explore what caused them, and consider how you can avoid being fined for similar violations.
The biggest GDPR fines of 2020, 2021, and 2022 (so far)
1. Amazon — €746 million ($877 million)
Amazon’s gigantic GDPR fine, announced in the company’s July 2021 earnings report, is nearly 15 times bigger than the previous record. The full reasons behind the fine haven’t yet been confirmed, but we know the cause has to do with cookie consent.
And this isn’t the first time Amazon has been punished due to the way it collects and shares personal data via cookies. In late 2020, France fined Amazon €35 million after the tech giant allegedly failed to get cookie consent on its website.
How the fine could have been avoided: It’s tempting to force users to “agree” to cookies—or make opting out of cookies difficult—to collect as much personal data as possible. But regulators have shown some serious appetite for enforcing the EU’s cookie rules recently. If Amazon had obtained “freely given”, informed, and unambiguous opt-in consent before setting cookies on its users’ devices, the company probably could have avoided this huge GDPR fine.
4. Facebook — €265 million ($275 million)
Facebook owner Meta was fined €265 million ($275 million) by the Irish Regulator the Data Protection Commission for breaching data protection rules after it was revealed that Facebook personal data had been made available on an online hacking forum. This included the full names, phone numbers, birth dates and locations of Facebook users using the site in 2018 and 2019.
How the fine could have been avoided: Meta admitted the data had been scraped using legitimate tools designed to help people find their friends through their phone numbers. Facebook was fined for “failing to apply Data Protection by Design and Default” as stipulated by the EU update to General Data Protection Regulation (GDPR). Designing this function to be more secure would have avoided the fine.
2. WhatsApp — €225 million ($255 million)
Mere months after Amazon’s colossal GDPR fine knocked Google off the number one GDPR fine spot, WhatsApp pushed Google into third place with a penalty nearly five times as large as the search giant’s previous record. Ireland slammed WhatsApp with A €225 million GDPR penalty after claiming that the messaging service had failed to properly explain its data processing practices in its privacy notice.
Ireland is not known for issuing large fines, despite being the European home of nearly every US-based big tech firm. And even this penalty arrived only after other EU data protection authorities used the “one-stop-shop” mechanism to argue that it should have been higher. So what did WhatsApp do wrong? It’s complicated, and the company is appealing the decision.
But it boils down to WhatsApp’s alleged failure to explain its legal basis for certain data processing—“legitimate interests.”
How the fine could have been avoided: The Irish DPA said that WhatsApp’s somewhat opaque privacy notice was at fault here—the company should have provided privacy information in an easily accessible format using language its users could understand. If you’re relying on “legitimate interests,” you must make sure you explain what those interests are in respect of each relevant processing operation.
3. Google Ireland — €90 million ($102 million)
The French data protection authority (the CNIL) hit Google Ireland with this substantial fine on Jan 6 2022. The fine relates to the way Google’s European arm implements cookie consent procedures on YouTube. The Google Ireland fine was one of two fines issued as part of the same decision, with the other being levied against California-based Google LLC (which operates Google Search).
So what’s the issue? In a nutshell, the CNIL said that Google should have made it easier for YouTube users to refuse cookies. YouTube sets cookies on our devices to track our online activity for marketing purposes. It’s easy to accept cookies on YouTube, but harder to refuse them. The CNIL noted that refusing cookies required a user to make several clicks, whereas accepting cookies required just one click.
The CNIL justified the relatively high fine by pointing to the large number of people using YouTube and the huge profits that Google derives from the service. But wait a minute—doesn’t Google run its EU operations out of Ireland? How come the Irish regulator didn’t deliver this fine?
The reason, the CNIL contended, is that cookie regulation primarily falls under the ePrivacy Directive, not the GDPR, so regulators can take direct action against website operators in their jurisdiction rather than referring everything back to the organization’s “main establishment.” But the decision still qualifies as a “GDPR fine” because it’s the GDPR that determines how website operators obtain consent.
How the fine could have been avoided: Under the GDPR, consent must be “freely given”: equally easy to accept or refuse: if you can accept with one click, you should also be able to refuse with one click.
4. Facebook (again) — €60 million ($68 million)
This fine came from the French data protection authority, the CNIL, on Jan 6, 2022. The social media giant earned this €60 million penalty owing to—you guessed it—failing to obtain proper cookie consent from its users.
The issue here mainly related to the unclear way in which Facebook provided a cookie opt-out. Like with Google (see above and below), accepting cookies on Facebook is a piece of cake—just click “accept.” Refusing them is a little more complicated.
How the fine could have been avoided: The CNIL drew attention to how Facebook’s cookie consent interface seemed to offer no option except “Accept Cookies”—even when it appeared that users were actually refusing them. The CNIL reflected that this language” necessarily generates confusion and that the user may have the feeling that it is not possible to refuse the deposit of cookies and that they have no way to manage it. Don’t confuse your users. Keep language simple and straightforward whenever you’re providing privacy information.
5. Google LLC — €60 million ($68 million)
This Jan 6 fine against Google’s California headquarters came alongside the CNIL’s €90 million penalty against the search giant’s European establishment (see fine number 3, above). That larger sanction was levied against Google’s non-compliant setting of cookies on the YouTube platform.
Google LLC was hit with this €60 million blow on the same day for precisely the same reason—but in relation to its search website rather than its video-sharing platform.
How the fine could have been avoided: The takeaway in both Google cases is clear: make sure it’s as easy for your users to accept cookie consent as it is for them to refuse it.
6. Google – €50 million ($56.6 million)
Google’s fine, levied in 2019 and finalized after an unsuccessful appeal in March 2020, was the largest on record until August 2021.
The case related to how Google provided privacy notice to its users—and how the company requested their consent for personalized advertising and other types of data processing.
How the fine could have been avoided: Google should have provided more information to users in consent policies and granted them more control over how their personal data is processed.
7. H&M — €35 million ($41 million)
On October 5, 2020 the Data Protection Authority of Hamburg, Germany, fined clothing retailer H&M €35,258,707.95 — the second-largest GDPR fine ever imposed at the time.
H&M’s GDPR violations involved the “monitoring of several hundred employees.” After employees took vacation or sick leave, they were required to attend a return-to-work meeting. Some of these meetings were recorded and accessible to over 50 H&M managers.
Senior H&M staff gained ”a broad knowledge of their employees’ private lives… ranging from rather harmless details to family issues and religious beliefs.” This “detailed profile” was used to help evaluate employees’ performance and make decisions about their employment.
How the fine could have been avoided: H&M appears to have violated the GDPR’s principle of data minimization — don’t process personal information, particularly sensitive data about people’s health and beliefs, unless you need to for a specific purpose.
H&M should also have placed strict access controls on the data, and the company should not have used this data to make decisions about people’s employment.
8. TIM – €27.8 million ($31.5 million)
On January 15, 2020, Italian telecommunications operator TIM (or Telecom Italia) was stung with a €27.8 million GDPR fine from Garante, the Italian Data Protection Authority, for a series of infractions and violations that have accumulated over the last several years.
TIM’s infractions include a variety of unlawful actions, most of which stem from an overly aggressive marketing strategy. Millions of individuals were bombarded with promotional calls and unsolicited communications, some of whom were on non-contact and exclusion lists.
How the fine could have been avoided: TIM should have managed lists of data subjects more carefully and created specific opt-ins for different marketing activities.
9. Enel Energia — €26.5 million ($29.3 million)
On January 19th, 2022 the Italian data protection authority (‘Garante’) publicized its decision to fine the multinational electric and gas supplier Enel Energia €26.5 million for a range of GDPR violations including failing to get user consent or inform customers before using their personal data for telemarketing calls.
The complex investigation was triggered after Garante had received numerous complaints concerning the receipt of unwanted promotional calls among other problems. The investigation covered Enel Energia’s business partners and included four separate requests for cumulative information, from December 2018 to July 2020, concerning a total of 135 files. Garante also reported that Enel Energia had not sufficiently cooperated with the investigation by failing to respond adequately (if at all) to a number of requests.
How the fine could have been avoided: Enel Energia should have provided more information to users in consent policies and granted them more control over how their personal data is processed. Once caught out, Enel Energia could have also lessened the consequences had they responded to requests by investigators.
10. British Airways – €22 million ($26 million)
In October, the ICO hit British Airways with a $26 million fine for a breach that took place in 2018. This is considerably less than the $238 million fine that the ICO originally said it intended to issue back in 2019.
So, what happened back in 2018? British Airway’s systems were compromised. The breach affected 400,000 customers and hackers got their hands on log-in details, payment card information, and travelers’ names and addresses.
How the fine could have been avoided: According to the ICO, the attack was preventable, but BA didn’t have sufficient security measures in place to protect their systems, networks, and data. In fact, it seems BA didn’t even have basics like multi-factor authentication in place at the time of the breach.
Going forward, the airline should take a security-first approach, invest in security solutions, and ensure they have strict data privacy policies and procedures in place.
11. Marriott – €20.4 million ($23.8 million)
While this is an eye-watering fine, it’s actually significantly lower than the $123 million fine the ICO originally said they’d levy. So, what happened?
383 million guest records (30 million EU residents) were exposed after the hotel chain’s guest reservation database was compromised. Personal data like guests’ names, addresses, passport numbers, and payment card information was exposed.
Note: The hack originated in Starwood Group’s reservation system in 2014. While Marriott acquired Starwood in 2016, the hack wasn’t detected until September 2018.
How the fine could have been avoided: The ICO found that Marriott failed to perform adequate due diligence after acquiring Starwood. They should have done more to safeguard their systems with a stronger data loss prevention (DLP) strategy and utilized de-identification methods.
12. Clearview AI — €20 Million ($20.5 Million)
In what is shaping up to be a busy year for the Italian data protection authority, Clearview AI has been issued a fine of €20 Million by Garante. The fine came on 10 February 2022, after several issues in connection with Clearview’s facial recognition products.
A number of infringements were found including the unlawful processing of personal biometric and geolocation data, and the breaching of several fundamental principles of the GDPR, such as transparency, purpose limitation, and storage limitation. Like Enel Energia, the company also failed to respond to requests in a complete and timely manner.
How the fine could have been avoided: Less is more – Clearview should have only collected and held on to data with a clear purpose, and been transparent about this decision-making with their customers. Better co-operation in the investigation would have also decreased the fine.
13. Meta (Facebook) Ireland — €17 Million ($18.2 Million)
On March 15th, 2022 the Irish Data Protection Commission (DPC) fined Meta Platforms Ireland €17 Million for issues which meant it could not readily demonstrate the security measures that it implemented to protect EU users’ data. This failure was spotted in 2018 after twelve personal data breaches were reported to the DPC. This is the third fine of 2022.
How the fine could have been avoided: In this case, these shortcomings were spotted before a more widespread breach occurred. To prepare for future threats, Meta should take a security-first approach, invest in security solutions, and ensure they have strict data privacy policies and procedures in place.
14. Wind — €17 million ($18.2 million)
On July 13, Italian Data Protection Authority imposed a fine of €16,729,600 on telecoms company Wind due to its unlawful direct marketing activities.
The enforcement action started after Italy’s regulator received complaints about Wind Tre’s marketing communications. Wind reportedly spammed Italians with ads — without their consent — and provided incorrect contact details, leaving consumers unable to unsubscribe.
The regulator also found that Wind’s mobile apps forced users to agree to direct marketing and location tracking and that its business partners had undertaken illegal data-collection activities.
How the fine could have been avoided: Wind should have established a valid lawful basis before using people’s contact details for direct marketing purposes. This probably would have meant getting consumers’ consent — unless it could demonstrate that sending marketing materials was in its “legitimate interests.”
For whatever reason you send direct marketing, you must ensure that consumers have an easy way to unsubscribe. And you must always ensure that your company’s Privacy Policy is accurate and up-to-date.
15. Vodafone Italia — €12.3 million ($14.5 million)
Vodafone Italia’s November 2020 fine was issued in relation to a vast range of alleged GDPR violations, including provisions within Articles 5, 6, 7, 16, 21, 25, 32, and 33.
So what did Vodafone do that resulted in so many GDPR violations?
The company’s data processing issues included failing to properly secure customer data, sharing personal data with third-party call centers, and processing without a legal basis—all brought to light after complaints about the company’s telemarketing campaign.
How the fine could have been avoided: Vodafone’s marketing operations may have triggered the Italian DPA’s investigation, but the company’s data management and security were the fundamental issues here.
Vodafone might have avoided this large fine by conducting regular audits of its data and properly documenting all relationships with third-party data processors.
16. Notebooksbilliger.de — €10.4 million ($12.5 million)
German electronics retailer notebooksbilliger.de (NBB) received this significant GDPR fine on January 8, 2021. The penalty relates to how NBB used CCTV cameras to monitor its employees and customers.
The CCTV system ran for two years, and NBB reportedly kept recordings for up to 60 days. NBB said it needed to record its staff and customers to prevent theft. The Lower Saxony DPA said the monitoring was an intrusion on its employees’ and customers’ privacy.
How the fine could have been avoided: The NBB’s fine reflects strict attitudes towards CCTV monitoring in parts of Germany. The regulator said NBB’s CCTV program was not limited to a specific person or period.
Using CCTV isn’t prohibited under the GDPR, but you must ensure it is a legitimate and proportionate response to a specific problem. The UK’s ICO has some guidance on using CCTV in a GDPR-compliant way.
17. Austrian Post — €9 million ($10.23 million)
Austria’s largest GDPR fine hit in September 2021, when Austrian Post received a €9 million sanction for allegedly failing to facilitate data subject rights requests properly.
If a data subject hoped to access, delete, or rectify personal data held by the Austrian Post, the company provided a variety of mediums by which to make a request, including a web form, mail, or phone number.
The one means of communication that Austria Post did not recognize, however, was email—and the Austrian DPA said that the mail carrier should have allowed data subjects to submit a rights request via any medium they preferred.
How the fine could have been avoided: Austrian Post (which is planning to appeal the fine) should have processed data subject rights requests however they arrived—forcing data subjects to use a particular communication method and excluding email is not an acceptable way to facilitate their rights.
18. Eni — €8.5 million ($10 million)
Eni Gas e Luce (Eni) is an Italian gas and oil company that was found to have made marketing phone calls without a proper legal basis.
While telemarketing is covered by the ePrivacy Directive, this is another example of how any processing of personal data without a proper legal basis can lead to a GDPR fine.
How the fine could have been avoided: Eni should have ensured it had a proper legal basis for telemarketing before calling any of its customers or leads. In this case, the Italian DPA said that the proper lawful basis would have been consent.
19. Vodafone Spain — €8.15 million ($9.72 million)
Vodafone’s €8.15 million fine, issued by the Spanish DPA (the AEPD) on March 11, 2021, is actually made up of four fines for violating the GDPR and other Spanish laws covering telecommunications and cookies. The Vodafone fine stands as Spain’s biggest yet—in a year that has seen the AEPD issue several substantial GDPR penalties. The fine results from 191 separate complaints regarding Vodafone’s marketing activity. Vodafone was alleged not to have taken sufficient organizational measures to ensure it was processing people’s personal data lawfully.
How the fine could have been avoided: Vodafone’s complex series of legal violations all appear to have one thing in common: a lack of organization and control over personal data used for marketing purposes.
Whenever you outsource any processing activity to a third party—for example, a marketing agency—you must ensure you have a clear legal basis for doing so. Keep clear records, maintain data processing agreements with contractors, and regularly audit your processing activities to ensure they are lawful.
19. REWE International — €8 Million ($8.8 Million)
The Austrian Data Protection Authority (DPA) has fined Austrian food retailer REWE International €8 million after the mismanaging of the data of users involved in its loyalty program, jö Bonus Club. The subsidiary had been collecting users’ data without their consent and using it for marketing purposes.
However, REWE is set to appeal the decision, arguing that jö Bonus Club operates independently as a separate subsidiary, Unser Ö-Bonus Club. This comes hot off the heels of a 2021 fine after jö Bonus Club unlawfully collected millions of members’ data and sold it to third parties. The offense saw jö Bonus Club pay €2 Million.
How the fine could have been avoided: There are a few things that could be done to stop these recurring fines – seeking consent from customers and applying the fundamental GDPR principles of transparency, purpose limitation, and storage limitation are good places to start.
20. Google – €7 million ($8.3 million)
From a GDPR enforcement perspective, 2020 was not a good year for Google.
Along with the company losing its appeal against French DPA in January, March saw the Swedish Data Protection Authority of Sweden (SDPA) fining Google for neglecting to remove a pair of search result listings under Europe’s GDPR “right to be forgotten” rules.
How the fine could have been avoided: Google should have fulfilled the rights of data subjects, primarily their right to be forgotten. This is also known as the right to erasure. How? By “ensuring a process was in place to respond to requests for erasure without undue delay and within one month of receipt.”
You can find more information about how to comply with requests for erasure from the ICO here.
21. Caixabank — €6 million ($7.2 million)
This fine against financial services company Caixabank is the largest fine ever issued by the Spanish DPA (the AEPD).
The AEPD finalized Caixabank’s penalty on January 13, 2021, breaking Spain’s previous record GDPR fine, against BBVA — issued just one month earlier. This suggests a significant toughening of approach from the Spanish DPA.
The first issue, which accounts for €4 million of the total fine, related to how Caixabank established a “legal basis” for using consumers’ personal data under Article 6. Second, Caixabank was fined €2 million for violating the GDPR’s transparency requirements at Articles 13 and 14.
How the fine could have been avoided: The AEPD said Caixabank relied on the legal basis of “legitimate interests” without proper justification. Before you rely on “legitimate interests,” you must conduct and document a “legitimate interests assessment.”
The company also failed to obtain consumers’ consent in a GDPR-compliant way. If you’re relying on “consent,” make sure it meets the GDPR’s strict “opt in” standards.
The AEPD criticized Caixabank’s privacy policy as providing vague and inconsistent information about its data processing practices. Make sure you use clear language in your privacy notices and keep them consistent across websites and platforms.
22. Cosmote Mobile Telecommunications — €6 Million ($6.6 Million)
In February 2022 the Greek data protection authority, the Hellenic Data Protection Authority (HDPA) fined Cosmote Mobile Telecommunications €6 Million.
The fine was issued after a hack in September 2020 led to customers’ private information being exposed, but the buck didn’t stop there. It was revealed that the company was illegally processing customer data – an activity that exacerbated the issues caused by the hack. To make matters worse, the private data was not fully pseudonymized, making it easier for hackers to identify individuals from the data.
Cosmote’s parent company, OTE group was then given an additional fine of €3.25 million after the Cosmote investigation determined that OTE should have been included in the process from the beginning but had not been.
How the fine could have been avoided: Unfortunately, this domino effect is not an uncommon occurrence that only highlights the importance of abiding by GDPR rules and principles. For a start, Cosmote should be only processing data legally, with purpose, and with proper encryption to ensure best customer security.
Secondly, this example demonstrates how devastating a hack can be. It has been reported that the hack that caused this breach was a phone hack – meaning secure internet connections, improved physical security and investing in security solutions are all good ways to prevent this from happening.
23. BBVA (bank) — €5 million ($6 million)
This fine against financial services giant BBVA (Banco Bilbao Vizcaya Argentaria) dates from December 11, 2020.
The BBVA’s penalty is the second biggest that the Spanish DPA (the AEPD) has ever imposed, and it shares many similarities with the AEPD’s largest-ever penalty, against Caixabank, issued the following month. Taken together with the record fine against Caixabank, it’s tempting to conclude that the Spanish DPA has its eye on the GDPR compliance of financial institutions.
How the fine could have been avoided: The AEPD fined BBVA €3 million for sending SMS messages without obtaining consumers’ consent. In most circumstances, you must ensure you have GDPR-valid consent for sending direct marketing messages.
The remaining €2 million of the penalty related to BBVA’s privacy policy, which failed to properly explain how the bank collected and use its customers’ personal data. Make sure you include all the necessary information under Articles 13 and 14 in your privacy policy.
24. Fastweb — €4.5 million ($5.5 million)
Italy’s DPA (the Garante) fined telecoms company Fastweb €4.5 million on April 2 2021 for engaging in unsolicited telephone marketing without consent. In particular, the Garanta noted that Fastweb was using “fraudulent” telephone numbers that the company had not registered with Italy’s Register of Communication Operators.
How the fine could have been avoided: Fastweb’s fine derives from telemarketing rules that are set out in Italy’s implementation of the ePrivacy Directive, rather than the GDPR. However, the company still appears to have violated the GDPR by failing to obtain valid consent.
It’s important to remember this interplay between the EU’s main privacy laws. The ePrivacy Directive requires you to obtain consent for certain activities, but the GDPR sets the standard of consent—and the standard is very high.
25. Dutch Tax and Customs Administration — €3.7 Million ($4 Million)
In April 2022, The Dutch Tax and Customs Administration was fined €3.7 Million after the illegal processing of personal data in the Fraud Signaling Facility (FSV) – a blacklist on which the Tax and Customs Administration kept records of fraud. For more than six years, the Tax and Customs Administration had been wrongly putting people on the FSV – around 270,000 people in total – with major consequences for those on the list. The investigation revealed a number of GDPR violations including widespread discrimination, with employees instructed to base the risk of fraud in part on people’s appearance and nationality.
“People were often wrongly labeled as fraudsters, with dire consequences,” Dutch Data Protection Authority Chairman Aleid Wolfsen said in a statement. “The tax authorities have turned lives upside down with FSV.”
This is the highest fine that the Dutch Data Protection Authority (AP) has ever imposed, and reflects the seriousness of the violations as well as the number of people affected and the timespan over which the violations occurred.
How the fine could have been avoided: In this extraordinary case, the issues spread beyond data security, with intent and impact both being malicious. It looks like The Dutch Tax and Customs Administration could do with brushing up on not just GDPR rules, but discrimination and equality laws as well.
26. Eni Gas e Luce — €3 million ($3.6 million)
This fine is one of two imposed on the Italian gas and oil company Eni in December 2019. This is a complicated case involving the creation of new customer accounts—but it boils down to the failure of Eni to obey the GDPR’s principle of accuracy.
How the fine could have been avoided: Data protection is about more than just privacy—it also covers issues like records management. Eni should have ensured its customer records were kept accurate and up-to-date.
27. Capio St. Göran AB — €2.9 million ($3.4 million)
Capio St. Goran is a Swedish healthcare provider that received a GDPR fine following an audit of one of its hospitals by the Swedish DPA. The audit revealed that the company had failed to carry out appropriate risk assessments and implement effective access controls. As a result, too many employees had access to sensitive personal data.
How the fine could have been avoided: Conducting a data protection impact assessment (DPIA) is mandatory under the GDPR for controllers undertaking certain risky activities or handling large-scale sensitive data.
Eni should have conducted such an assessment to determine which staff required access to medical records. Access to sensitive personal data should be restricted to those who strictly require it.
28. Iren Mercato — €2.85 million ($3.4 million)
In June 2021, the Italian DPA fined energy company Iren Mercato for carrying out a telephone marketing campaign without obtaining proper consent. The phone calls were conducted by a third party marketing company acting as a data processor.
How the fine could have been avoided: Many of the fines on our list relate to telemarketing and the failure to obtain GDPR-valid consent.
Remember that even when using third-party services to conduct marketing campaigns, you could still be directly liable under the GDPR if you fail to establish a valid legal basis for processing personal data.
29. Foodinho — €2.6 million ($3 million)
Groceries delivery service Foodinho received this substantial fine in June 2021, after the Italian DPA found the company had failed to obey the GDPR’s rules on “automated processing,” in this case the use of an algorithm to determine employees’ wages and workflow.
The company was also found to have violated the GDPR’s principle of “lawfulness, fairness, and transparency” by failing to provide employees with adequate information.
How the fine could have been avoided: Foodinho’s fine mainly relates to a relatively niche area of GDPR compliance—”solely automated processing with legal or similarly significant effects.”
In short, if you’re making purely AI-driven decisions about people that could impact on their finances, employment, or access to services, you must ensure you provide a human review of such decisions.
30. National Revenue Agency (Bulgaria) — €2.6 million ($3 million)
This August 2019 fine against Bulgaria’s National Revenue Agency was issued after the organization suffered a data breach affecting 5 million people. The breached data included people’s names, contact details, and tax information. The Bulgarian DPA found that the agency failed to take effective technical and organizational measures to protect the personal data under its control.
How the fine could have been avoided: The Bulgarian National Revenue should have conducted a thorough risk assessment of its processing operations and taken effective steps to safeguard personal data.
While it’s not clear what caused this data breach, it’s worth noting that the FBI’s Internet Crime Control Center cites email as the number one threat vector in cybercrime. By securing your company’s email systems, you’re cutting off one of your major vulnerabilities and significantly reducing the likelihood of a data breach.
What else can organizations be fined for under GDPR?
While the biggest fines involve marketing activities, failure to remove personal data when requested by EU citizens, and unlawfully requiring employees to have their biometric data recorded, there are a number of ways in which a breach can occur.
In fact, so far this year, misdirected emails have been the primary cause of data loss reported to the ICO. But, how do you prevent an accident? By focusing on people rather than systems and networks.
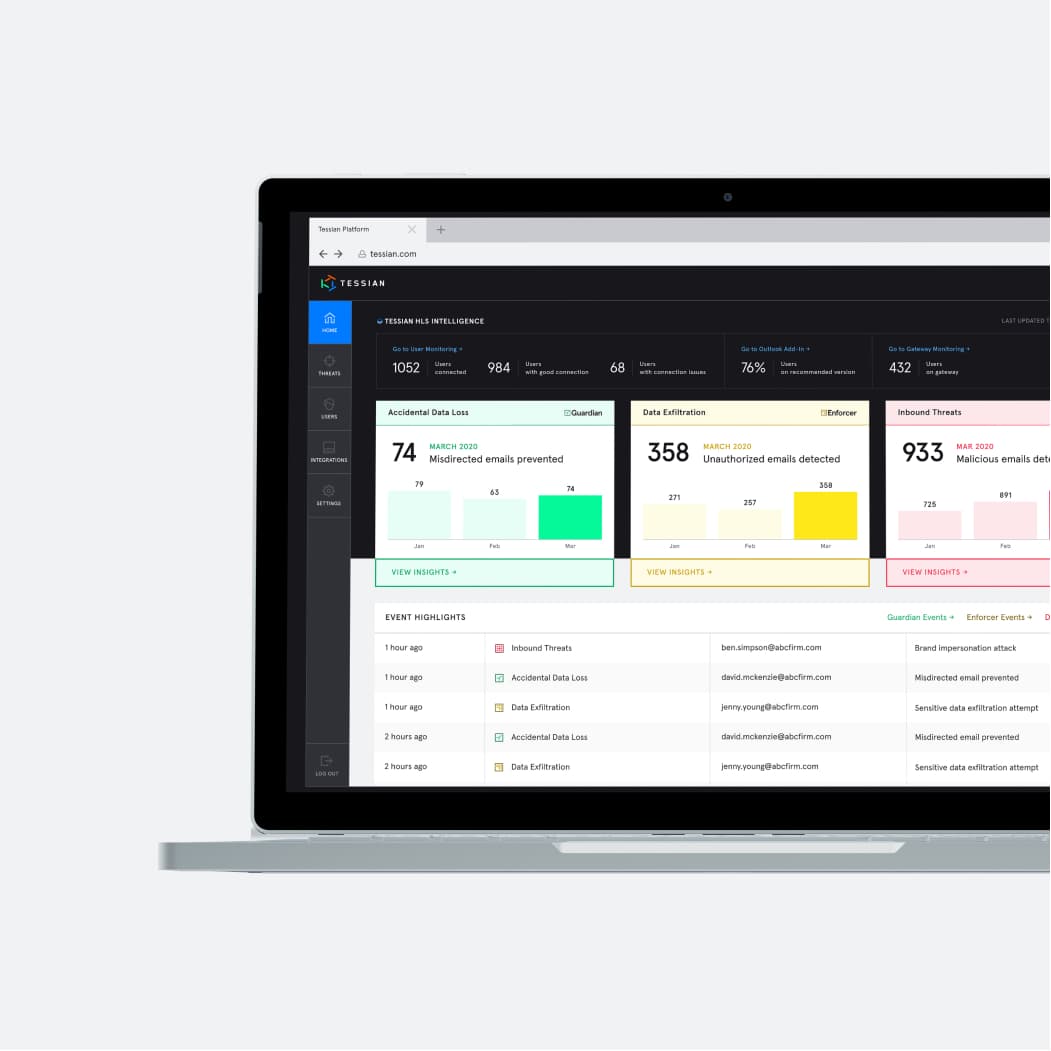
How does Tessian help organizations stay GDPR compliant?
Powered by machine learning, Tessian understands human behavior and relationships, enabling it to automatically detect and prevent anomalous and dangerous activity, including misdirected emails. Tessian also detects and prevents spear phishing attacks and data exfiltration attempts on email.
Importantly, though, Tessian doesn’t just prevent breaches. Tessian’s key features – which are both proactive and reactive – align with the GDPR requirement “to implement appropriate technical and organizational measures together with a process for regularly testing, assessing and evaluating the effectiveness of those measures to ensure the security of processing” (Article 32).
To learn more about how Tessian helps with GDPR compliance, you can check out this page, our customer stories or book a demo.