Secure Email Gateways (SEGs) vs. Integrated Cloud Email Security (ICES) Solutions
Recent market developments in email security signal there is a new player in town. And what has been considered a solved-for cybersecurity challenge is receiving renewed attention, both in the enterprise and in the analyst community.
The next generation of email security, referred to by Gartner as Integrated Cloud Email Security (ICES) solutions, bring a welcome and new approach to solving for increasingly sophisticated and elusive email security threats.
Advanced threats require a new approach to addressing email security risk
Threat actors are using more sophisticated techniques, and attacks are achieving greater success. This is largely due to the commercialization of cybercrime, with Phishing-as-a-Service and Ransomware-as-a-Service offerings becoming more prevalent on the dark web.
The pace of digital transformation underway and key shifts in the way we work help explain it, too. In the wake of the pandemic, the accelerated adoption of public cloud has significantly expanded attack surface risk, with employees working from home, and often on personal devices.
Threat actors are exploiting these developments by targeting the most common threat vector for a breach, phishing via email.
Secure Email Gateways (SEGs)
SEGs were, until recently, considered a staple in the cybersecurity stack. But SEGs that run on static, rule-based detection engines are finding it increasingly challenging to protect in today’s threatscape. This is largely due to SEGs relying on adversaries exploiting common and well-known attack vectors.
SEG solutions sit in-line and filter all inbound emails. SEGs use a threat intelligence engine that is combined with manual policy orchestration, creating “allow” or “deny” lists. In the world of SEGs, security administrators have to configure MX records, develop specific emails security policies, block domains, and triage incidents – with many of these incidents false positives due to its “wide-net” email filtering approach.
Given the threat engine for SEGs also relies on known threats, it can enable threat actors to bypass SEG controls, for example, by registering new domains which are combined with advanced impersonation techniques. That’s why Tessian saw 2 million malicious, inbound emails evade SEGs in a 12-month period.
And once an adversary has compromised an organization’s email (i.e. passed through the gateway) there is little stopping them. SEGs also offer very limited protection against insider threats or advanced methods for email based data exfiltration, for example renaming document file names to bypass manual orchestrated SEG DLP policy labels.
The key attributes of SEGs include:
Designed to protect against commonly seen threats i.e. mainstream phishing activity, malware and spam
The redirection of mail via MX records pointing to the SEG to scan all incoming email
Using a sandbox for detecting, isolating, and detonating suspected malicious emails or attachments
Clawback ability for internal email only
No ability to detect lateral movement by a threat actor that has breached the gateway
Supplemental scanning solutions are often required to detect advanced inbound threats
Manual orchestration of basic DLP policies
Integrated Cloud Email Security (ICES) Solutions
The main distinguishing characteristic of ICES solutions like Tessian compared to SEGs, is that ICES solutions were born in the cloud, for the cloud. But, they’re also able to provide protection for hybrid and on-premise environments.
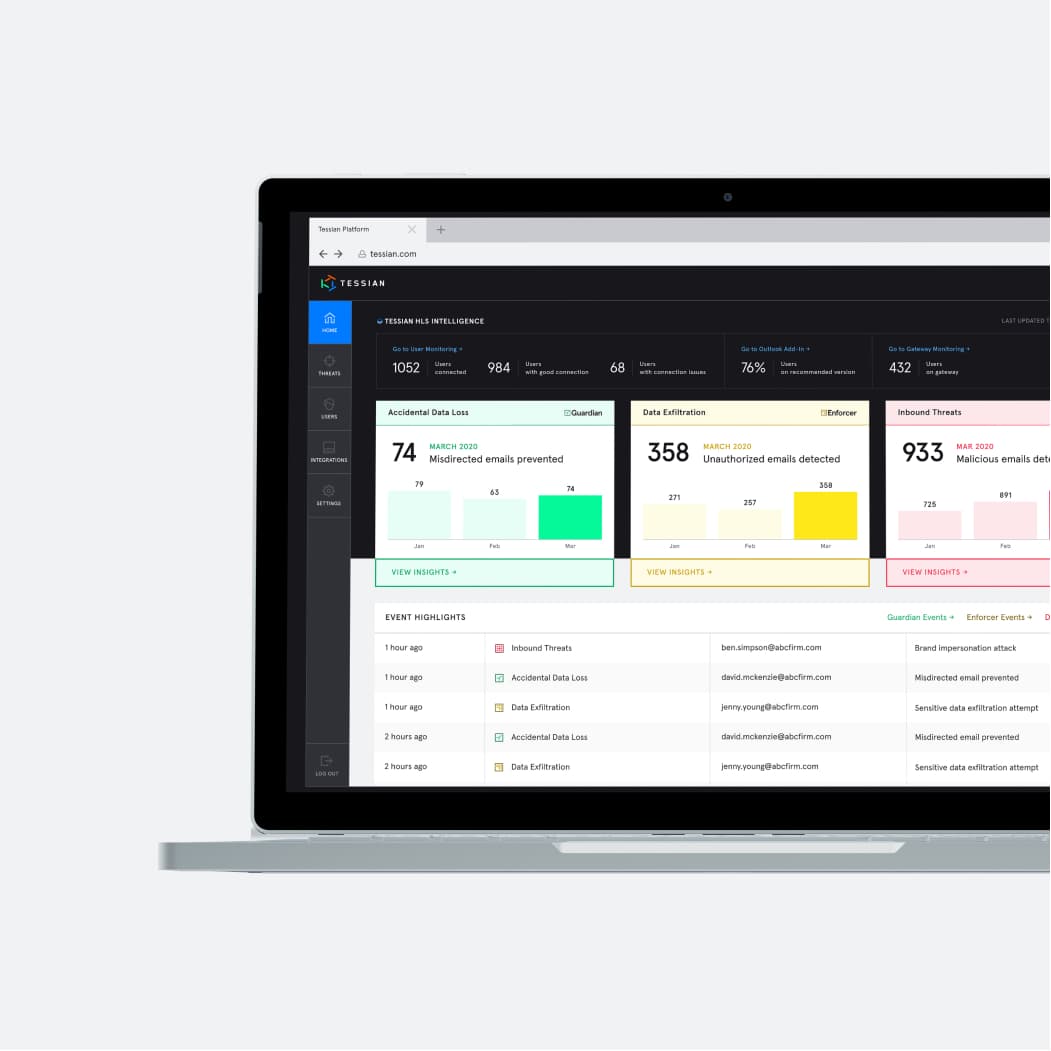
Using machine learning and connecting via connectors or an API, the algorithm of an ICES solution develops a historical behavioral map of an organization’s email ecosystem. This historical behavioral map is leveraged along with Natural Language Processing (NLP) and Natural Language Understanding (NLU) capabilities, to dynamically, and in-real-time, scan and detect any anomalous email behavior on both the inbound and the outbound side.
ICES solutions also offer a high degree of email security automation, including triaging of security incidents, which significantly reduces the SOC burden and ultimately improves security effectiveness.
The key attributes of ICES solutions include:
Designed to detect advanced social engineering attacks including phishing, impersonation attacks, business email compromise (BEC), and account takeover (ATO)
Require no MX record changes and scan incoming emails downstream from the MX record, either pre-delivery via a connector, or post-delivery via an API
Behavioral detection engine for advanced inbound and outbound threats, resulting in greater detection efficacy and lower false positives i.e. less business interruption and more SOC optimization
A banner can be added to an incoming email indicating the level of risk of the scanned email
Lateral attack detection capability
Malicious emails are hidden from users’ inboxes. With the pre-delivery option, only email that is determined to be safe is delivered. Post-delivery solutions will claw-back a suspected email determined to be malicious
All of the email fields are analyzed and compared against a historical mapping of email correspondence. Fields scanned include the sender, recipient, subject line, body, URL and attachments
Prompts the end-user with in-the-moment contextual warnings on suspected malicious emails to take safe action, in real-time
Some have advanced DLP capability
The evolution of the threatscape combined with the mainstream adoption of public cloud offerings and associated productivity suites, helps contextualize the emergence of the ICES vendor category.
Many of the productivity suites such as Microsoft 365 and Google Workspace include SEG-like features as part of their standard offerings. And Gartner predicts that by 2023, 40% of enterprises will be leveraging an ICES solution like Tessian with a public cloud’s productivity suite for comprehensive email protection.
Want to learn more? See how Tessian prevents ransomware attacks, and protects against DLP, watch a product overview video, download our platform architecture whitepaper, or book a demo.